
UNX-OBP
Unexpected Outbound Protocol (UNX-OBP)Unexpected Outbound Protocol (UNX-OBP)
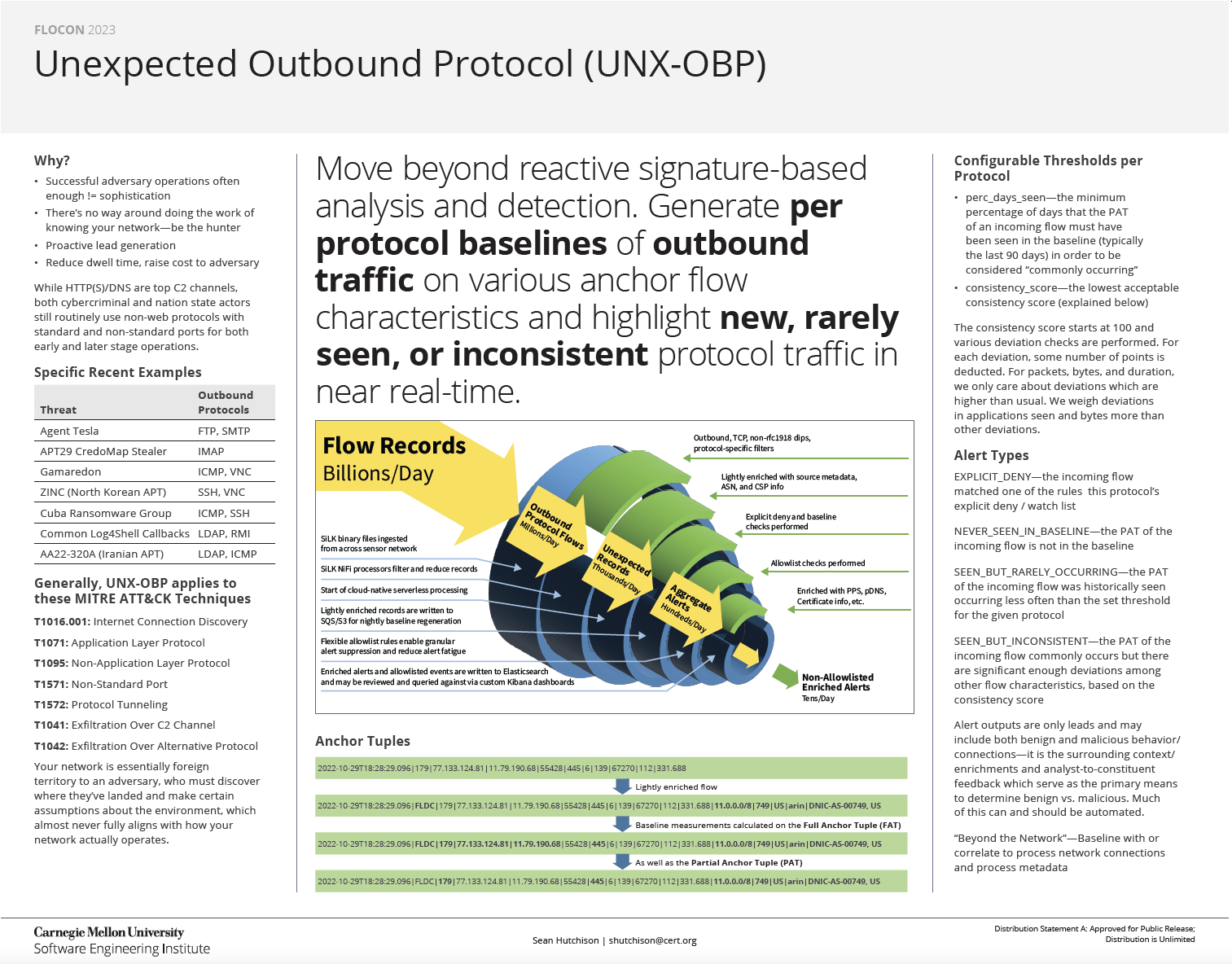
A basic Least Frequency of Occurrence (LFO) and anomaly based analytic/defensive layer that enables defenders to better know their network and force adversaries to really blend in by highlighting new, rarely seen, and/or inconsistent outbound protocol use.
Use to reduce the search space for a threat hunt, not as a means of high-fidelity detection.
Description
Target outbound protocols/datasets which meet the following criteria:
Is TCP or ICMP-based because we cannot reliably determine outbound org asset-initiated flows of UDP-based protocols with SiLK-based uniflow
Has YAF application label support
Is not super high volume and/or has naturally very diverse destinations, like web traffic - such protocols/datasets require more targeted analytics. However, you may onboard more discrete/smaller sets of such protocol traffic (e.g. HTTP on non-standard ports, SSL/TLS on non-standard ports, etc.)
Good candidates for onboarding include but are not limited to SMB, FTP, SSH, RDP, VNC, LDAP, HTTP on non-standard ports, etc.
Highlight unexpected outbound traffic occurring at both early and later stages of attacks:
Various ports/protocols may be specified within initial exploits/payloads (e.g. Log4Shell) or leveraged for command and control (C2) in later stage callbacks or exfiltration
Highlight new and/or rarely seen combinations of sensors, destination ports, and destination netblocks/ASNs per protocol
Highlight unexpected/inconsistent traffic per protocol, particularly with regard to new application layer use and significant deviations in volume of outbound data transfer
“We are already seeing malware families such as Redline Stealer, QakBot, and Nanocore be successful despite their use of random and non-standard ports. This prohibits traditional, full internet scanning as it is not feasible to scan all possible non-standard ports across the IPv4 space. While once thought to be easier to detect, the use of high ports seems to still be an adequate C2 communication channel, and we predict that more C2 operators will make use of high ports for their C2 communication.” -Recorded Future 2022 Adversary Infrastructure Report
There are many more real-world examples from both less and more advanced threat actors. You should know when this happens.
Project Notes
The Terraform resources provided here allow you to quickly create a self-contained prototype deployment to see and test how this works. It is NOT for production.
This is a self-contained prototype. It’s probably better to perform enrichments and alert suppression via integrations and automated workflows with a SIEM/SOAR platform. Feel free to do that.
For quick deployment, see Get Started.
For a manual deployment, review and adjust the Terraform as necessary, considering notes and initial load steps in Component Details.
FloCon 2023 Poster
License
Released under a MIT (SEI)-style license, please see LICENSE or contact permission@sei.cmu.edu for full terms.
[DISTRIBUTION STATEMENT A] This material has been approved for public release and unlimited distribution.
